Effective vendor management tools has emerged as an ingredient of successful business operations in the current market environment where there is interdependence among the markets. The advanced software solutions are being sought more and more by organizations to manage the intricacies of third-party partnerships. Most of the best vendor management tools in the market today provide holistic services, which have changed the way businesses assess, track and engage their out-of-house suppliers. These are vendor management tools that are integrated with automation, artificial intelligence, and real-time monitoring to assist business to reduce risks, facilitate compliance, and streamline performance of vendors throughout the entire supply chain ecosystem.
What Are Vendor Management Tools?
The vendor management tools are specific software platforms that are aimed to assist the organisations in managing their interactions with third parties in terms of service providers and suppliers throughout the entire lifecycle of the partnership. These solutions automate such important processes as a vendor selection, performance evaluation, risk assessment, contract administration, and compliance monitoring. The best vendor management tools allow organizations to make sound decisions, minimize operational efficiencies, and have more robust and transparent relationships with its third-party vendors and remain compliant with regulations.
Essential Features to Look for in Vendor Management Tools
When choosing the appropriate vendor management tools, it is important to take into account the features that would suit the organizational needs and objectives.
- Automated Risk Assessment: The current modern platforms must have artificial intelligence and machine learning to constantly test the security posture of the vendor, their financial health, and compliance status and provide dynamic risk scores that are updated with real-time information and threat progressions.
- Compliance Tracking Capabilities: Find the tools that provide automated compliance with the industry requirements and internal policies and assure that the vendors use the standards, such as GDPR, ISO 27001, HIPAA, or SOC 2, by automatically gathering documentation and managing the audit trail.
- Real-Time Monitoring Systems: Continuous monitoring operations allow that monitors the performance metrics of vendors, security vulnerabilities, and change in operations help identify the possible problems before they arise into massive problems to your business operations.
- Information Repository: A central database where all the documentation of the vendors, contracts, evaluations, and information history are stored makes it easier to access important information and make better decisions across business teams.
- Reporting and Analytics Dashboard: The detailed visualization tools that provide the information about the vendor performance, risk trends, and compliance metrics in the easily digestible manner can help the stakeholders to understand the vendor environment and, therefore, make strategic decisions.
Comparison Table for Top 10 Vendor Management Tools
| Tool Name | Rating | Best Feature |
| Panorays | 4.5/5 | Continuous 24/7 security monitoring |
| SecurityScorecard | 4.6/5 | Proprietary A-F security grading system |
| ComplyScore® by Atlas Systems | 4.7/5 | AI-powered compliance automation |
| UpGuard Vendor Risk | 4.4/5 | Dark web data breach detection |
| Black Kite | 4.5/5 | Ransomware Susceptibility Index® |
| Connecteam | 4.3/5 | Venminder Exchange assessment marketplace |
| ServiceNow Vendor Risk Management | 4.6/5 | Integrated enterprise risk correlation |
| OneTrust Third-Party Management | 4.4/5 | Seamless privacy and security integration |
| Archer | 4.2/5 | Customizable dashboards and reporting |
| SAP Fieldglass | 4.3/5 | External workforce management capabilities |
Top 10 Vendor Management Tools
1. Panorays

Rating: 4.5/5
Website: https://panorays.com/
Best Use Cases: Organizations requiring continuous cybersecurity monitoring and automated vendor assessments
Panorays provides an all-encompassing method of handling third-party cybersecurity risks by automating and being intelligent. With this platform, organizations gain the power to assess and monitor the security positions of their vendors through a continuous process that does not need a lot of manual intervention. Through external threat intelligence, customized questionnaires, and technical scanning, Panorays can help businesses have insights into their vendor ecosystem that can be acted on. Risk DNA feature of the solution is dynamic and changes the risk rating based on various data sources so that the organization is continuously informed of the security status of its third-party partners.
Key Features
- Round-the-clock security surveillance
- Customizable automated questionnaires
- Dynamic Risk DNA scoring
- Vendor collaboration portal
- Real-time threat alerts
Pros
- Instant vulnerability notifications
- Pre-configured compliance templates
- Streamlined vendor communication
Cons
- Limited penetration testing depth
- Narrow cybersecurity focus only
- Complex customization for beginners
Pricing: Custom pricing
Also Read: Best Financial Management Tools
2. SecurityScorecard
Rating: 4.6/5
Website: https://securityscorecard.com/
Best Use Cases: Enterprises needing standardized security ratings and supply chain threat intelligence
SecurityScorecard is the latest application transforming vendor cybersecurity rating systems in organizations because it has a unique rating system that provides letter ratings ranging between A and F. The strategy makes even complex security measurements easy to understand and presents in measures that can be easily understood and can be quickly understood by all the stakeholders at all tiers.
The platform performs constant checks on the change of vendors and gives in-depth analytical information on the certain types of vulnerabilities. SecurityScorecard allows companies to understand the risks in their supply chains beyond direct vendors into longer chains and thus it is invaluable when the business has a complex network of vendors and needs to be aware at all times.
Key Features
- Letter-grade security ratings are assigned to SICOR.
- Constant monitoring of the posture.
- The tools of supply chain intelligence.
- Collaboration portal.
- The complete metric dashboards.
Pros
- Visualization of security.
- The power of external threat identification.
- Cooperation with vendors.
Cons
- Excessive use of questionnaires.
- Inaccurate rating at times.
- Complexity of the advanced features.
Pricing: Custom pricing
3. ComplyScore by Atlas Systems
Rating: 4.7/5
Website: https://www.atlassystems.com/complyscore
Best Use Cases: Regulated industries requiring strict compliance adherence and automated risk scoring
ComplyScore is the predominant vendor management app to be applied to the organizations in the highly-regulated sectors in the healthcare, finances, and shops. The sophisticated artificial intelligence algorithms in the platform compare the vendors to tailored needs like cybersecurity readiness, regulatory compliance, and financial stability.
ComplyScore 2 is used by companies in more than 65 countries and fits well with a broad variety of foreign regulatory regimes. Its machine learning solutions can autonomously identify and react to accidents, and save squads considerable amounts of time on authoring compliance verifications and risk overview handiwork and improve precision and reliability.
Key Features
- AI-driven risk scoring
- The workflows of automated governance.
- Incident management of machine learning.
- Regulatory alignment in the world.
- Active identification of vulnerabilities.
Pros
- Assistance of international regulation.
- Design oriented on compliance.
- Very responsive customer care.
Cons
- Learning Curve Advanced feature Learning.
- Premium pricing structure
- Complicated starting arrangement.
Pricing: Custom pricing
4. UpGuard Vendor Risk
Rating: 4.4/5
Website: https://www.upguard.com/product/vendor-risk
Best Use Cases: Organizations prioritizing data breach prevention and continuous vendor security monitoring
UpGuard Vendor Risk offers broad coverage of the third-party security vulnerabilities in the form of continuous monitoring and assessment. The unique advantage of the platform is its data breach detection system that will scan public data leaks as well as dark web sources to warn organizations in case sensitive information is compromised.
UpGuard offers precise risk assessments through automated risk assessment, that is, using artificial intelligence, to help businesses comprehend their risk environment in the context of vendors. The security rating system of the solution provides standardized measurements of vendor comparisons, whereas guided remediation processes assist the partners in correcting the vulnerabilities that have been identified in a systematic and efficient manner.
Key Features
- Dark web breach detection
- AI-powered automated assessments
- Continuous security scanning
- Unlimited vendor support
- Guided remediation workflows
Pros
- Scalable enterprise integrations
- Standardized security ratings
- Systematic risk remediation
Cons
- Complex initial setup process
- Occasional data update delays
- Higher cost for small businesses
Pricing: Free
5. Black Kite

Rating: 4.5/5
Website: https://blackkite.com/
Best Use Cases: Businesses requiring deep supply chain visibility and ransomware risk assessment
Black Kite goes to extensive and unparalleled levels of vendor cybersecurity assessment with its technical, data-driven risk evaluation method. This platform, unlike most competitors, does not only look at direct vendors but further extends the focus to the fourth, fifth, and even sixth parties in supply chains. The proprietary Ransomware Susceptibility Index, is a distinctive look at the vulnerability of vendors to ransomware attacks, which allows proactive defensive against such actions.
The cloud asset mapping features provided by Black Kite scan the infrastructure of vendors operating in multi-cloud environments and detect configuration vulnerabilities and security loopholes. The financial risk quantification capabilities of the platform assist the executives to know the financial implications of possible cases of cybersecurity breaches, so that they can make more sound decisions regarding resource allocation.
Key Features
- Extended party risk monitoring
- Cloud infrastructure mapping
- Ransomware susceptibility scoring
- FocusTags™ threat tracking
- Financial impact quantification
Pros
- Actionable financial insights
- Rapid automated assessments
- Real-time event tracking
Cons
- Complex workflow configuration
- OSINT data limitations
- Premium feature expenses
Pricing: Custom pricing
6. Connecteam
Rating: 4.3/5
Website: https://connecteam.com/
Best Use Cases: Organizations seeking complete vendor lifecycle management and assessment exchange capabilities
Connecteam offers full vendor management services including initial onboarding, all the way through offboarding, and structured control over the course of partnerships. Through its exclusive Connecteam Exchange marketplace, organizations are able to procure earlier executed vendor evaluations, which allows the due diligence process to be highly expedited and saves organizations, which have replicated evaluation tasks.
Its Venmonitor™ continuous monitoring capability ensures that business is updated with real-time scenarios during the change of vendor risk profiles. Connecteam will offer customizable assessment templates which will be in compliance with key frameworks such as NIST and ISO so as to have a comprehensive evaluation of inherent and residual risks. The full functionality of the feature renders it especially useful to those companies that have complicated compliance needs.
Key Features
- Assessment exchange marketplace
- Venmonitor™ continuous tracking
- Complete lifecycle management
- Customizable risk templates
- Framework-aligned evaluations
Pros
- Accelerated assessment processes
- Comprehensive regulatory alignment
- Structured governance approach
Cons
- Vendor data dependency
- Complex implementation process
- Feature overload for small companies
Pricing: Custom pricing
Explore More Reading Pieces: Best Application Whitelisting Tools to Prevent Malware
7. ServiceNow Vendor Risk Management
Rating: 4.6/5
Website: https://www.servicenow.com/uk/
Best Use Cases: Large enterprises requiring integrated risk management and vendor performance tracking
ServiceNow Vendor Risk Management effectively incorporates third-party risk evaluation into the wider enterprise risk management systems, offering the organization-wide view of risks. Through the platform, businesses are able to match the threats associated with vendors to the rest of the operational, financial and strategic threats in order to have an all-round risk intelligence.
Its vendor tiering functions enable organizations to categorize the partners based on the level of risk, so that reasonable resource distribution and intensity of control are achieved. The vendor portal will enable an efficient coordination between organizations and their partners and the flow of information and evaluation will be simplified. Advanced reporting and analytics features help to convert raw data into meaningful insights which can be used to make strategic decisions on all levels of the organization.
Key Features
- Vendor collaboration portal
- Automated assessment questionnaires
- Comprehensive analytics reporting
- Vendor tiering classification
- Integrated risk correlation
Pros
- Holistic risk visibility
- Priority-based resource allocation
- Real-time performance tracking
Cons
- Occasional performance slowdowns
- Complex platform implementation
- Advanced customization difficulty
Pricing: Free
8. OneTrust Third-Party Management
Rating: 4.4/5
Website: https://www.onetrust.com/
Best Use Cases: Organizations wanting unified privacy, security, and vendor governance management
OneTrust Third-Party Management is quite superior in that it combines vendor risk assessment with other larger privacy, security, and governance programs to establish a single ecosystem of compliance. It is a platform that automates risk evaluation services; therefore, consistency and a lot of manual work are eliminated. The unified vendor site puts all related information of the partners into a single accessible place that is easy to manage in terms of data.
The regulatory compliance tracking offered by OneTrust tracks the requirements of different industries and jurisdictions and makes sure that the vendors comply with the relevant standards. This data is processed by the AI-based insights of the platform which analyze the data patterns of the vendors to determine potential threats before they occur to allow proactive measures that prevent the organizational interests through mitigation.
Key Features
- Automated risk evaluations
- Concentrated vendor store.
- Tracking of regulatory compliance.
- Artificial intelligence-based foresight.
- Integration of modules functionality.
Pros
- Single-market integration with OneTrust.
- This is due to vast educational material.
- Predictive risk analytics
Cons
- Problems of non-standard integration.
- Complex initial setup
- Dependency of vendors.
Pricing: Custom pricing
9. Archer
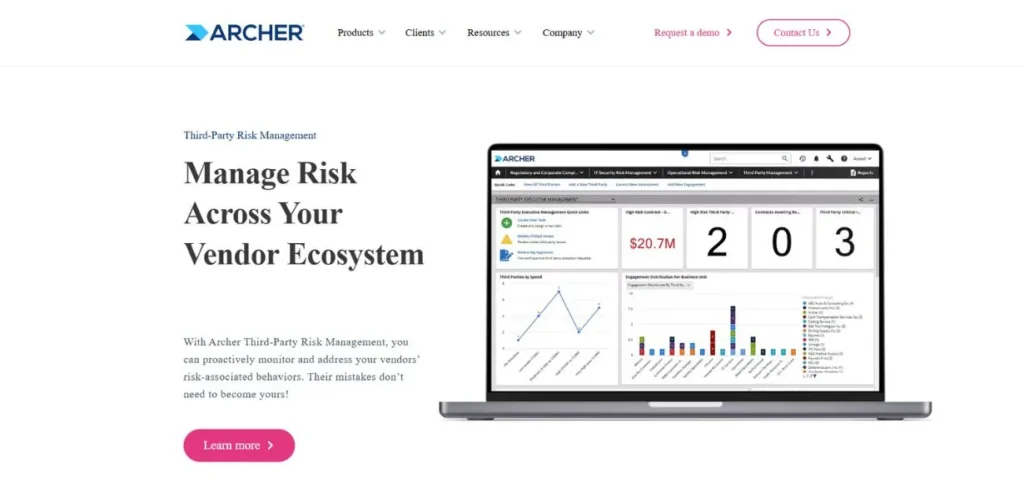
Rating: 4.2/5
Website: https://www.rsa.com/
Best Use Cases: Financial institutions with complex vendor ecosystems requiring comprehensive risk management
Archer, which belongs to the RSA Archer Suite, offers vendor management of enterprise scale especially that is well applied in organizations with complex relationships with third parties. The central vendor repository is a powerful database that keeps a track of all the vendor data effectively in a single place. Reporting instruments and customizable dashboards provide an understanding of risk measurements and the performance of vendors according to the particular organizations.
The risk scoring methodology by Archer involves the use of fixed parameters to give the vendor rating and constantly watch the risk posture. The platform is integrated with the contract management systems to monitor the obligations and terms of the agreements with vendors so as to ensure cooperation during partnership periods.
Key Features
- Vendor database is centralized.
- Custom-made dashboard reporting.
- Continuous risk scoring
- Integration of contract management.
- Background congruency of the frameworks.
Pros
- Hardly cognitive operational dashboards.
- Good regulatory compliance.
- Tracking of contract obligation.
Cons
- Complex user interface
- Financial services focus
- Lack of plug-and-play capability.
Pricing: Custom pricing
10. SAP Fieldglass
Rating: 4.3/5
Website: https://www.sap.com/india/index.html
Best Use Cases: Global enterprises managing external workforce and service procurement operations
SAP Fieldglass offers cloud-based vendor management and is specifically tailored to the firms that are intensive users of external talent and outsourced services. The platform simplifies the processes of vendor onboarding, management, and offboarding besides maintaining compliance and cost optimization during partnerships. Its contract management and performance tracking features encourage better relationship with the supplier and transparency and accountability.
The compliance management properties ensure that industry laws and internal policies are tracked automatically and would help reduce possible risks of regulatory breach. The SAP Fieldglass can help in the process of procurement of services through offering solutions to manage contracts and Statements of Work and thus it is a necessity to enterprises that have high requirements of contingent workforce.
Key Features
- External workforce management
- Performance tracking systems
- Automated compliance monitoring
- Service procurement facilitation
- Contract and SOW management
Pros
- Powerful third-party integrations
- Extensive feature set
- Simplified data management
Cons
- Mobile app limitations
- Integration connection difficulties
- Initial complexity for users
Pricing: Custom pricing
How to Choose the Right Vendor Management Tool
Among the best vendor management tools, you must be serious and consider the specifics of your organization, existing infrastructure, and strategies.
- Assess Your Industry Requirements: There are different regulatory concerns and risk profiles of different industries, that necessitate the special features.
- Test Scalability and Flexibility- As your organization grows in size and size, you will have more or less vendor management needs, and so will your vendor ecosystem.
- Consider Integration Capabilities: The present business world is marked by the advanced technology system comprised of fragmented tools that create information silos and inefficiency.
- Compare Cost and Value: Cost limits are critical but lowest price is not the way to offer the best value in the long run when it comes to vendor management.
- Test User Experience and Support: The number of features that a platform has is no use; it will not work when the users feel that it is too complicated, or they do not receive enough support when implementing it and working on a daily basis.
Conclusion
The complexity of the relationship between the third party requires certain advanced tools that integrate automation, intelligence, and round-the-clock surveillance. The optimal vendor management tools, which were described below, offer a range of functions, which may satisfy most organizational needs, such as both advanced compliance automation and deep cybersecurity testing and lifecycle management.
Whether compliance with regulations, managing risks or running operations is your number one priority, investing in a strong vendor management software will strengthen partnerships, prevent threats and keep your organization on the path of sustainable development. Be aware in respect to aligning your own uniqueness with the capability of each platform to create a solution that suits your vendor governance strategy.
Frequently Asked Questions
Q: What are the main advantages of applying vendor management tools?
A: They are automated risk assessment platforms, regulator compliance, offer 24/7 visibility of the vendor performance and security posture, centralized data, documentation and communication, and allow data-driven decision-making via full-fledged analytics and reporting.
Q: What are the benefits of vendor management tools in the area of compliance?
A: They automatically follow regulatory requirements across jurisdictions, track compliance standards by vendors, are able to maintain audit trails and create compliance reports and inform organizations of possible violations before they occur and lead to penalties or business interruptions.
Q: Is vendor management tool helpful to small businesses?
A: Absolutely. Even though certain enterprise solutions can be too much, there are numerous solutions that have smaller versions or are custom priced to offer small businesses the necessary risk assessment, compliance monitoring, and vendor management capabilities, depending on their size and complexity.
Q: What then is the distinction between vendor risk management and vendor performance management?
A: Vendor risk management is aimed at uncovering, evaluating, and eliminating potential risks of third-party relationships such as security threats, compliance risks, and financial risks. Performance management monitors the metrics of operations such as service quality, timeliness, and conformity to the contract to streamline the relations with vendors.
Q: What frequency of assessing the vendors?
A: Continuous monitoring is possible using the best vendor management tools that update the risk assessment in real-time depending on the new information. Nevertheless, thorough manual inspections are likely to be conducted once a year in the case of low-risk suppliers, once a quarter in the case of medium-risk partners, and once a month or even more often in case of high-risk critical suppliers.
Continue To Explore More: Top Data Classification Tools